Shadow IT governance for AI agents has become the defining enterprise security challenge of 2026 — and most organisations are losing the battle before they even know it has started. What began as a quiet workaround — a team building a quick app over a weekend, a marketer connecting an AI tool to the CRM without IT approval — has escalated into a full-scale architectural crisis. According to Gartner, 41% of employees are now classified as citizen developers, building or customising applications outside formal IT oversight. The consequences are severe: IBM’s 2024 Cost of a Data Breach Report places the average breach cost at $4.88 million — and Shadow IT is one of the leading contributing factors.
In the rapidly evolving landscape defined by Agentic Workflows and the Universal Commerce Protocol (UCP), the stakes have never been higher. If your enterprise has not yet built a formal shadow IT governance framework for AI agents, you are not just behind — you are ex posed.
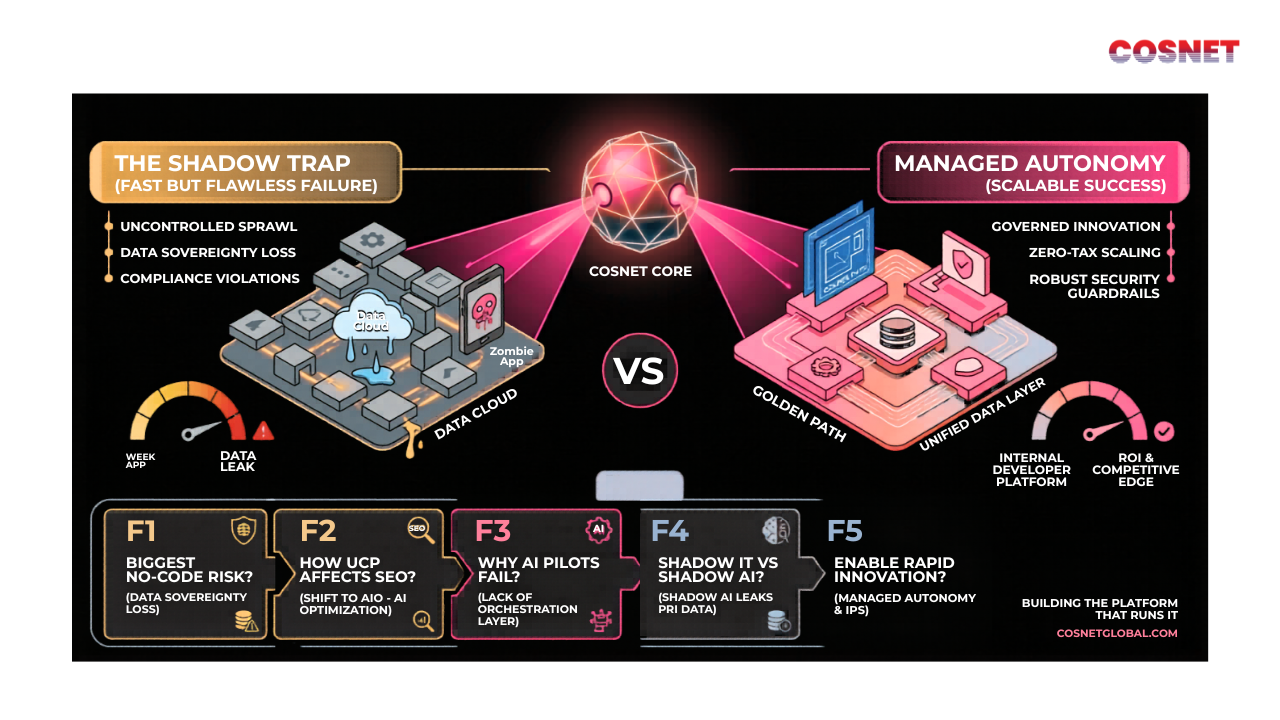
Why Shadow IT Governance for AI Agents Is the #1 Security Risk of 2026
The rise of Low-Code and No-Code platforms has fundamentally changed who builds software inside an organisation. Tools like Zapier, Power Apps, Make (formerly Integromat), and dozens of AI-native platforms allow non-technical teams to build functional applications in hours — bypassing the traditional software development lifecycle entirely.
On the surface, this looks like a productivity revolution. In reality, it is a governance time bomb.
When a marketing team builds a customer data pipeline in a no-code tool connected to a public AI API, three things happen simultaneously:
- Proprietary customer data leaves the approved security perimeter
- IT has no visibility into what data is going where
- The application has no documentation, no patching schedule, and no disaster recovery plan
This is what Gartner calls a “Zombie App” — undocumented, unpatched, and invisible to the central security stack. And in 2026, as AI agents begin operating autonomously across these same pipelines, the attack surface expands exponentially.
A 2025 Cisco report found that 65% of enterprise security leaders identify Shadow IT as a top-three security concern. Yet fewer than 30% have a formal governance framework in place to address it. That gap is exactly where breaches happen.
The problem is no longer theoretical. In 2024 alone, multiple high-profile enterprise breaches were traced back to unapproved AI tools handling sensitive customer data — tools that had never been reviewed, audited, or even catalogued by central IT. When the speed of deployment outpaces Enterprise Software Security, the result is not innovation. It is a massive, invisible technical debt that IT departments can no longer track.
The Hidden Cost of Low-Code Sprawl: Zombie Apps and Data Sovereignty Loss
Beyond the immediate security risk, Low-Code sprawl creates a deeper, more systemic problem: the loss of your organisation’s single Source of Truth.
Every time a team builds an unauthorised application to solve a localised problem, they create a new data silo. Over time, these siloes multiply — each one containing a fragment of your customer records, transaction history, or operational data. None of them communicate with each other. None of them are compliant. And none of them are visible to your IT or data governance teams.
This is the Data Sovereignty crisis at the heart of modern enterprise Shadow IT.
What data sovereignty loss actually costs your organisation:
When mission-critical data lives in a third-party “black box,” your organisation loses the ability to:
- Audit who accessed what data and when
- Respond to GDPR, CCPA, or DPDPA data subject access requests
- Prove compliance during a regulatory audit
- Detect when sensitive data has been exfiltrated
The legal and financial consequences are significant. GDPR fines can reach €20 million or 4% of global annual turnover — whichever is higher. In India, the Digital Personal Data Protection Act (DPDPA) 2023 is now fully in force, with penalties reaching up to ₹250 crore for serious violations.
Beyond regulatory risk, Low-Code sprawl creates what engineers call Technical Debt — the accumulated cost of shortcuts that eventually demand to be fixed. A “weekend app” built in a no-code tool may solve a problem today, but six months later it becomes a maintenance burden that no one in IT knows how to manage, update, or safely decommission.
At Cosnet, our Data Analytics services help enterprises build unified data architectures that eliminate these siloes — giving every department the visibility it needs without compromising central governance.
Shadow IT vs Shadow AI: Understanding the Critical Difference
In 2026, the conversation has evolved beyond traditional Shadow IT into a newer, more dangerous variant: Shadow AI.
While Shadow IT refers broadly to any unauthorised software used within a company, Shadow AI specifically refers to employees using unapproved AI tools — or building unapproved AI “wrappers” — to handle company data.
The distinction matters because the risk profile is fundamentally different:
| Shadow IT | Shadow AI | |
|---|---|---|
| What it is | Unauthorised apps and tools | Unapproved AI tools and custom GPT wrappers |
| Primary risk | Data silos, compliance gaps | Data poisoning, IP leakage to public models |
| Detection difficulty | Medium | High — AI interactions leave minimal audit trails |
| Remediation complexity | Medium | Very high — prompts may contain trade secrets |
| Speed of spread | Weeks to months | Hours to days |
The most dangerous aspect of Shadow AI is what security researchers call Data Poisoning — where an employee feeds proprietary business logic, client data, or internal processes into a public AI model. Once that data has been submitted as a prompt to an external model, it may become part of that model’s training data. Your trade secrets effectively become part of the public domain.
This is not a theoretical risk. It is happening today, in enterprises of every size, across every industry.
Cosnet’s AI Agents Development practice is specifically engineered to build AI integrations that keep your data sovereign, auditable, and fully within your governance perimeter — so your teams can use AI at full power without leaking what makes your business valuable.
From Shadow IT to Managed Autonomy: The Cosnet Framework
The instinctive response to Shadow IT is to block it. Lock down access. Restrict permissions. Force all software requests through a lengthy IT approval process.
This approach fails — every time.
It fails because the underlying need that drove the Shadow IT adoption is still there. Teams need to move fast. They need tools that work. If the approved options are too slow, too expensive, or too complicated, people will find workarounds. Blocking creates resentment without solving the problem.
At Cosnet, our engineering philosophy is built around a fundamentally different model: Managed Autonomy.
Managed Autonomy means giving teams the speed and flexibility they need to innovate — but within a pre-approved, secure architectural framework. Think of it as building a highway instead of a wall. People can still move fast. But they can only move fast in the right direction, on a road that has been engineered for safety.
The Cosnet Managed Autonomy framework rests on three core pillars:
Pillar 1: Standardised Golden Paths
A Golden Path is a pre-approved, FAANG-standardised blueprint for building applications within your organisation. Instead of leaving teams to discover tools independently — and inevitably choosing something insecure — you provide a curated catalogue of approved tools, APIs, AI models, and integration patterns.
A well-designed Golden Path:
- Includes pre-vetted AI tools and no-code platforms that meet your security standards
- Provides templates and starter kits so teams can move just as fast as they would with shadow tools
- Integrates automatically with your central monitoring and audit stack
- Is maintained and updated by a dedicated Internal Developer Platform (IDP) team
The result is that innovation does not slow down — it simply happens inside your security perimeter instead of outside it. Teams get the autonomy they want. IT gets the visibility it needs. Everyone wins.
Pillar 2: Centralised Data Orchestration
The second pillar addresses the data sovereignty problem directly. High-performance AI systems require a unified data layer — a single, governed repository that all applications, AI agents, and analytical tools connect to.
This centralised architecture means that even when different departments build their own front-end tools and AI workflows, the sensitive data underneath remains in a single, auditable location. Every access event is logged. Every data movement is tracked. Every AI agent interaction is recorded.
Cosnet’s AI Services practice specialises in designing these centralised orchestration layers — building the infrastructure that allows your AI agents to operate powerfully without ever operating blindly.
This approach also directly supports compliance. When every data access flows through a single governed layer, producing an audit trail for GDPR, DPDPA, or SOC 2 compliance becomes a reporting exercise rather than a forensic investigation.
Pillar 3: Automated Compliance Monitoring
The third pillar transforms governance from a manual process into an automated one.
Traditional IT governance relies on periodic audits — someone reviews the approved software list once a quarter and checks for violations. In an era where new AI tools can be connected and disconnected in minutes, this approach is hopelessly outdated.
Automated compliance monitoring means deploying systems that continuously scan your network for unauthorised integrations, flag new AI tool connections in real time, and automatically quarantine or escalate suspicious data flows before a breach can occur.
Using techniques from our Data Analytics practice — including ML-powered anomaly detection and intelligent log analysis — Cosnet builds compliance monitoring systems that audit themselves, so your security posture improves continuously rather than degrading between review cycles.
Is your enterprise exposed to Shadow IT risks? Book a complimentary AI governance assessment with Cosnet and find out exactly where your vulnerabilities are — before someone else does. Book Your Free Assessment →
How UCP Changes Shadow IT Governance for AI Agents in 2026
The emergence of the Universal Commerce Protocol (UCP) adds an entirely new dimension to the shadow IT governance conversation — one that most enterprise security teams have not yet considered.
UCP is Google’s open standard for AI-native commerce. It is a machine-readable protocol that allows AI shopping agents to interact directly with product and service data, bypassing traditional web browsing entirely. In the UCP era, AI agents do not visit websites. They query structured data endpoints.
This has a profound implication for shadow IT governance: if an unauthorised AI agent or no-code integration is connected to your product catalogue, pricing engine, or inventory system, it could be feeding incorrect, outdated, or sensitive data directly to external AI shopping agents — without any human review, and without any audit trail.
The potential consequences include:
- Incorrect pricing exposed to competitor AI agents
- Out-of-stock inventory presented as available, damaging customer experience
- Sensitive supplier pricing leaked through unaudited data endpoints
- Your products becoming completely invisible to AI shopping agents because the data structure does not meet UCP standards
Shadow IT governance for AI agents in the UCP era is therefore not just a security issue — it is a revenue issue. An unaudited, unstructured data environment will cost you customers you never knew you lost, through channels you never knew were being monitored.
For a deeper dive into how UCP is reshaping digital infrastructure, read our full analysis: Universal Commerce Protocol and What It Means for SEO.
The Real Cost of Inaction: What a Shadow IT Breach Costs in 2026
Numbers make the stakes concrete. Here is what enterprises face when shadow IT governance fails:
Direct financial costs:
- Average cost of a data breach: $4.88 million (IBM Cost of a Data Breach Report, 2024)
- Average time to identify and contain a breach: 258 days (IBM, 2024)
- GDPR maximum fine: €20 million or 4% of global annual turnover
- India DPDPA maximum penalty: ₹250 crore
- Average ransomware payment: $2.73 million (Sophos State of Ransomware, 2024)
Indirect costs that rarely make the headlines:
- Customer trust erosion — 66% of consumers say they would stop using a company after a data breach (Ping Identity, 2023)
- Talent attrition — security incidents increase employee turnover by up to 20%
- Stock price impact — publicly listed companies see an average 7.5% stock decline following a major breach (Comparitech)
- Competitor intelligence leakage — proprietary business logic fed into public AI models cannot be recovered
The question enterprises need to ask is not “can we afford to implement shadow IT governance for AI agents?” The real question is: “can we afford not to?”
The Strategic Verdict
Speed is only a competitive advantage when it is sustainable.
The era of “it worked on my machine” and “we will fix the governance later” is over. As businesses transition to Agentic Workflows — where AI agents operate autonomously, make decisions, and interact with external systems without human intervention at every step — the architecture underneath must be rock-solid.
The organisations that will win in the AI era are not the ones that move fastest. They are the ones that move fast without breaking things. That requires Managed Autonomy: an engineering philosophy where innovation is not blocked, but channelled through a secure, scalable, governed framework.
Eliminating the shadow IT crisis does not mean stopping innovation. It means engineering a platform where Digital Transformation can finally scale without compromising the foundation it is built on.
The three steps every enterprise should take this quarter:
- Audit your current Shadow IT exposure — catalogue every unauthorised tool, AI agent, and no-code application currently in use across all departments
- Establish your Golden Path — define the pre-approved tools, AI models, and architectures your teams can use freely without IT intervention
- Deploy automated monitoring — stop relying on periodic audits and start monitoring in real time, before a breach forces your hand
Cosnet is here to help with all three. Contact our engineering team for a complimentary Shadow IT governance assessment tailored to your organisation’s specific exposure.
FAQs: Shadow IT Governance for AI Agents
1. What is the biggest risk of Shadow IT in a Low-Code/No-Code environment?
The primary risk is Data Sovereignty loss. While Low-Code platforms enable rapid deployment, they routinely bypass Enterprise Software Security protocols, creating Shadow Data siloes. When sensitive customer information is stored in unauthorised third-party applications, IT departments lose the ability to track, audit, or protect that data — making the organisation highly vulnerable to compliance violations, regulatory fines, and security breaches. According to IBM, breaches originating from Shadow IT take an average of 258 days to detect and contain.
2. How does the Universal Commerce Protocol (UCP) affect Shadow IT governance?
UCP marks the shift from traditional web browsing to AI-native commerce. In the Agentic era, AI shopping agents interact directly with structured data endpoints rather than browsing websites. If unauthorised Shadow IT applications are connected to your product or pricing data, they may be feeding incorrect or sensitive information to external AI agents — creating both security and revenue risks simultaneously. Proper shadow IT governance for AI agents ensures your data endpoints are audited, structured, and fully UCP-compliant.
3. Why do AI pilots often fail when moving to a production environment?
Most AI infrastructure projects fail after the pilot phase because they were built as lightweight “wrappers” rather than truly integrated systems. A successful demo requires a clean prompt and a controlled dataset. A scalable AI strategy, however, requires a robust Orchestration Layer capable of handling real-world data noise, high concurrency, and Prompt Drift. Without professional engineering, the ROI on AI investment quickly disappears due to high latency, unpredictable API costs, and data integrity failures at scale.
4. What is the difference between Shadow IT and Shadow AI?
Shadow IT is an umbrella term for any unauthorised software used within an organisation. Shadow AI specifically refers to employees using unapproved AI tools or building custom AI wrappers to handle company data. The critical additional risk with Shadow AI is Data Poisoning — where proprietary business logic or client data is inadvertently fed into public AI models, potentially becoming part of that model’s training data and placing your trade secrets permanently in the public domain.
5. How can enterprises enable rapid innovation without compromising security?
The answer is Managed Autonomy — shifting from a “block everything” mentality to a model that channels innovation through secure, pre-approved frameworks. By establishing Internal Developer Platforms (IDPs) with Golden Paths, enterprises give teams the speed and flexibility they need while ensuring every new tool remains fully visible to the central security stack and aligned with the organisation’s broader AI governance strategy. Cosnet specialises in designing and deploying these frameworks for enterprises across India, the US, UK, and Sweden.
Ready to secure your AI infrastructure and eliminate shadow IT risk? Talk to a Cosnet engineer today — complimentary Shadow IT governance assessment available for qualifying enterprises.